For the longest time, Apple Airport Extreme secured the Dismal Manor networks. This began back in 2002 when, out of curiosity, the Head Moocher bought an Air Port Express to add WiFi in the early days. The Moocher had noticed that firmware updates kept showing up for the Airport products so concluded, rightly, that Apple was making an effort to keep these products up to date and secure. When Apple discontinued the Airport product line, it was time to move on. But to what?
Revisions
- Change featured image to UniFi Controller Dashboard View.
References
The following references may be useful but verify the SDN Contrller firmware version before using them. It still requires UniFi SDN command line operations at the router console to configure site to site VPNs and disable SIP ALG. These tasks are a bit easier in the EdgeRouter product line.
- https://help.ubnt.com/hc/en-us/articles/236281367-UniFi-USG-How-to-Adopt-a-USG-into-an-Existing-Network
- https://community.ubnt.com/t5/UniFi-Routing-Switching/Disable-SIP-ALG-on-USG/td-p/1671570
- https://help.ubnt.com/hc/en-us/articles/360002426234-UniFi-USG-VPN-How-to-Configure-Site-to-Site-VPN
Some Alternative Product Lines
At about this time, the Moocher’s church was remodeling a new club house and needed networking. Google found us Ruckus and YouTube noodling found Ubiquity and UniFi.
The folks doing YouTube small network videos had a preference for Ubiquity EdgeRouter Lite so Dismal Manor started with that. The small network providers prefer the EdgeRouter over the USG because it is easier to configure a site to site ipSec VPN and easier to configure port forwarding for some use cases. Both product lines use the same underlying firmware but with different graphical and remote management interfaces. A single console command language serves both product lines.
For home and small office use, the USG is the preferred device because a single management interface covers the entire campus or building network including gateways, switches, and WiFi access points. USG provides integrated logging of network events for all 3 device categories and a single maintenance interface allows firmware updates and device restarts. Moving to the switch management view allows reset of individual switch ports.
Managed or Unmanaged?
There is a fork in the road that you must negotiate early on, managed or unmanaged networking? An unmanaged network (the stuff off the shelf at Best Buy or Office Depot) is designed for specific use cases. This hardware is easily configured for a home LAN, a home WiFi having access to the LAN, and a guest WiFi having access only to the Internet. This meets most family needs.
Small office managed networks offer
- More sophisticated access control
- Activity logging, particularly network logins and login attempts
- Guest network acceptable use message
- Multiple WiFi access points
- Multiple WiFi networks (like one for Nest products) with restricted access to the LAN.
- WiFi client migration from one access point to its neighbor as the client moves about.
Business Models
Managed network equipment suppliers seem to have one of two business models.
- Sell the management capabilities as a licensed component on a yearly license.
- Bundle the management capabilities with the hardware.
Cisco, Dell, HP Aruba Networks, Juniper, Ruckus, etc are firmly in the first camp. Their products require the management kit and a high priest to look after them. Firmware updates are available by subscription only.
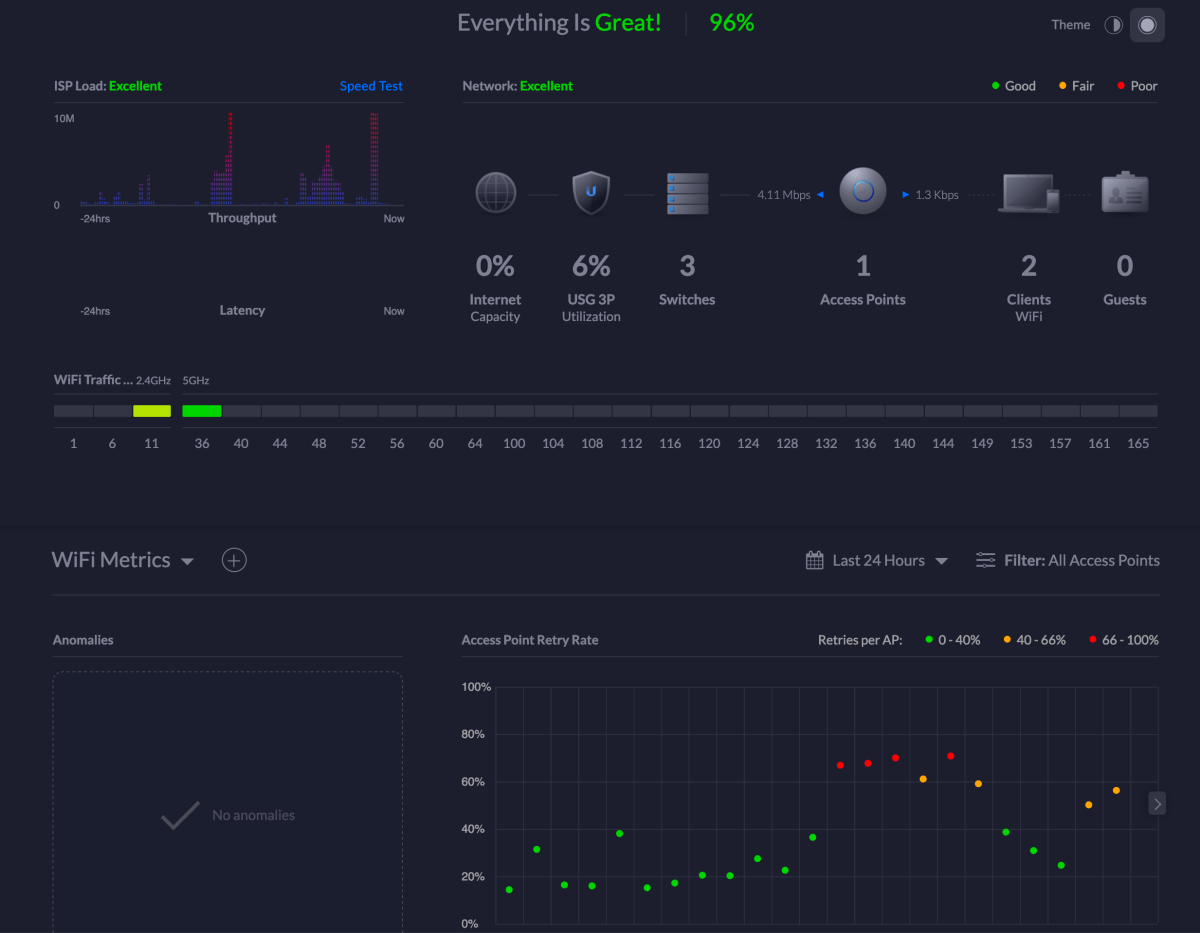
Ubiquity is in the second camp. Ubiquity components can be managed using a web browser but, if you install a Cloud Key, Ubiquity UniFi’s management appliance, you have centralized management and logging with a level of effort only slightly greater than that of using unmanaged SOHO devices. With or without a Cloud Key purchase, firmware updates are provided with initial purchase for the life of the equipment. Ubiquity is pretty good at supporting retired products so changing WiFi and switch port standards are driving device replacement.
Ubiquity has since revised its website to separate products by use case rather than by device category or function. Previously, all routers were together and all switches were together. These are now separated into network operator and UniFi product lines.
Dismal Manor’s Objective System
Dismal Manor began using Apple home devices and migrated to an EdgeRouter Lite with a UniFi Switch-8-150 core switch to power the added dog garden cameras. Living with the EdgeRouter for a year or so, we quickly discovered that Ubiquity has two management islands, one for the professional wireless Internet service provider kit and one for the small campus kit in the UniFi product line. The system management components for one product line could not manage products from the other. This led the Moocher to set an all UniFi system as his goal.
Motivation — Unexplained WiFi Fades
So, this spring, repeated observation of the Orbi satellite disconnect warning and WiFi fades in the louge convinced the Moocher to replace the WiFi gear before WiFi 6 becomes available in 2020. Were they acts of Cox or acts of Orbi and the neighbors.
A second goal was to consolidate all of the management under the UniFi Cloud Key. Keeping UNMS working was a pain. Running a UniFi controller instance was a pain. The two had conflicting package dependencies so multiple versions had to be maintained in separate VMs. No fun. Buy a Cloud Key and let UniFi worry about it.
The second consequence of having a mixed Operator UNMS and premisis UniFi environment was that UNMS could not display the traffic analysis that EdgeRouter produced in detail. UNMS provided a simple display of the EdgeRouter’s deep packet inspection results similar to the summary display shown below. And IDS/IPS is not available in a UNMS environment. In a wireless ISP environment, separate devices would perform these important tasks.
By moving to USG, I could have better visibility into my network client behavior, identify strained components, and obtain the benefits of IDS and IPS without further hardware or software.
New WiFi
The moocher added a UniFi In Wall HD access point. He meant to pick the new one but didn’t look carefully at what he had clicked. He replaced a wall plate in the lounge with this AP and set up a new Dismal Manor network for it. The In Wall HP access point has good coverage of the south end of the house. WiFi is a bit week but stable in the north end about15 meters and several walls away. It was easy to configure a network having LAN access and a Guest Network with announcement and acceptable use policy agreement portal. These were configuration options in the installation work flow.
The new WiFi has been rock solid. The new access point easily supports 4 networks in a single network group. So far, Dismal Manor has defined use for 3, the Moocher’s lair, the DIsmal Guest network, and the Dismal Things network. Dismal Things will eventually serve the Nest devices, Ring Doorbell, Eve Home devices, etc.
UniFi Controller can go beyond 4 networks by adding a second network group. I’ve not researched the limit for an access point.
The New USG
In addition to replacing the WiFi, Head Moocher replaced the EdgeRouter Lite with a UniFi Security Gateway. The EdgeRouters were primarily routers implementing and enforcing the network access policy. The USG has a bit broader scope. In addition to serving as a router, the USG can perform intrusion detection and intrusion prevention services and detailed internal and external traffic analysis and reporting.
The advantage of being all UniFi is that the Cloud Key handles all logging (no syslog server needed), all alerting, updating of access points, updating of switches, updating of routers, and provides an NVR and camera management, and all traffic analysis. I expect it to pick up VoIP management duties as Ubiquity’s VoIP offerings evolve. I could retire the VMs that had been running these things when migration began.
The addition of the USG allowed the Moocher to do the following using the Cloud Key’s management dialogs.
- Enable deep packet inspection and track usage
- Enable automated intrusion detection and intrusion prevention.
- View usage statistics both internally and with the Internet
- Create VLANS
- Create port forwarding rules
Site to site ipSec VPN setup still requires use of Ubiquity command language. Use of commercial hosted VPN services is simple as these tunnel via HTTPS to a proxy server.
Network Statistics with USG and Cloud Key

The image shows the statistics that the Cloud Key can collect using the USG and UniFi switch features. In the Dismal Manor network, the Head Moocher has enabled deep packet inspection and Intrusion Prevention.
The individual line items are clickable and selection changes what is shown below. This makes it possible to see traffic type by host.
There is one frustration here. The statistics appear to show cumulative traffic since installation rather than daily or monthly totals. As you can see, Apple iCloud, Google Drive (for club file sharing), and BackBlaze are top talkers on our network. Below that come YouTube and the other video on demand services with Tidal and Qobuz bringing up the rear. Other views break this traffic down by host and even the Nest Protects and Nest Thermostat are tracked.
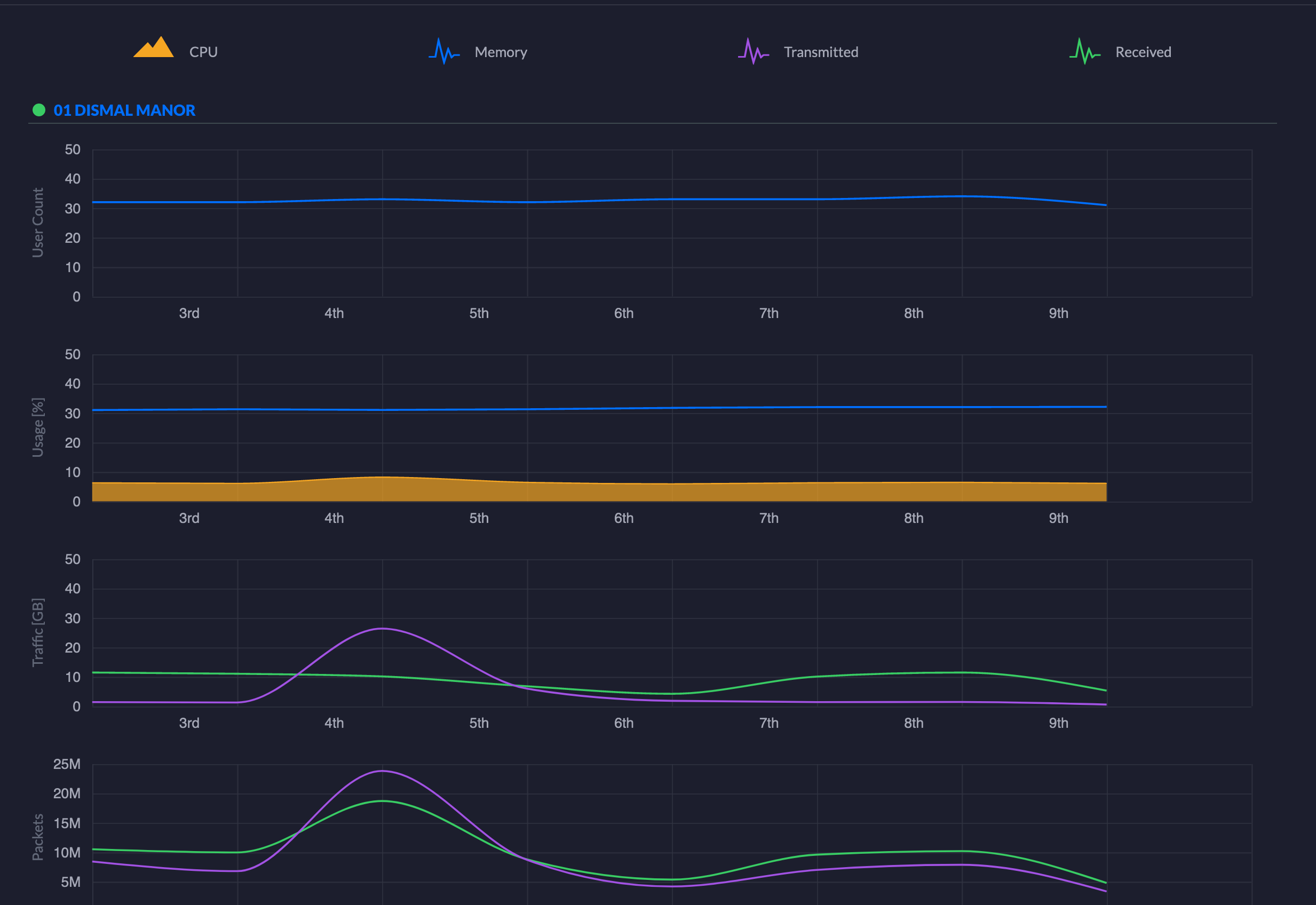
The figure above shows the USG’s processor and memory usage statistics over time. Our YouTube and overnight streamed audio show up here.
Additional displays break traffic down by hosts and by processes. This makes makes it easy to identify the source of congestion and take steps to mitigate congestion. This is important at Dismal Manor because we use the network to play high definition music recordings.
IDS and IPS are Quite, So Far
The Moocher enable IDS. No malicious activity detected. Because network performance was adequate in the presence of this additional workload on the router (85 mbps throughput), the Moocher enabled IPS which will close ports used for illegal activities. Though not quite wire speed, the USG is fast enough for the Dismal Manor network.
The USG’s response to external network mapping attempts is to drop ping requests. The search for open ports goes on continually so this activity is not shown. No external attacks have been detected so far.
Phishing is a far greater threat but the Moocher gets very suspicious when receiving a communication deviating from a correspondent’s normal behavior and communications policies. It is the Moocher’s practice to contact all correspondents directly rather than via links in Emails.
You must be logged in to post a comment.