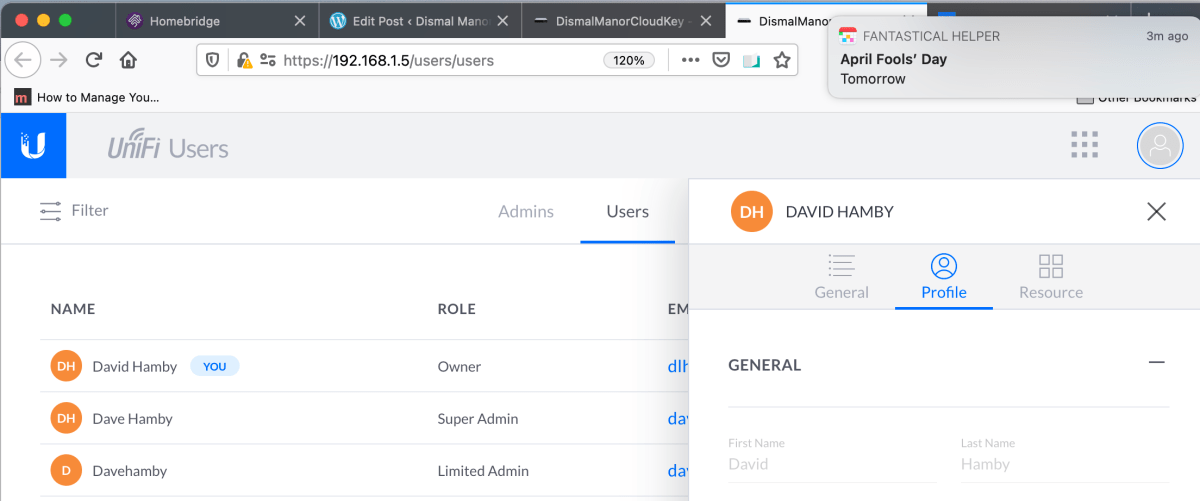
Recently, IT System Integrator forums and YouTube channels have been all a-twitter because it appeared that a UniFi user ID and network connection were required to use any of the UniFiOS hosted controllers introduced with along with UniFiOS. After hearing Tom Lawrence and Willie Howe rant about the issue, I decided to experiment a little to see if their complaint was true of my deployment.
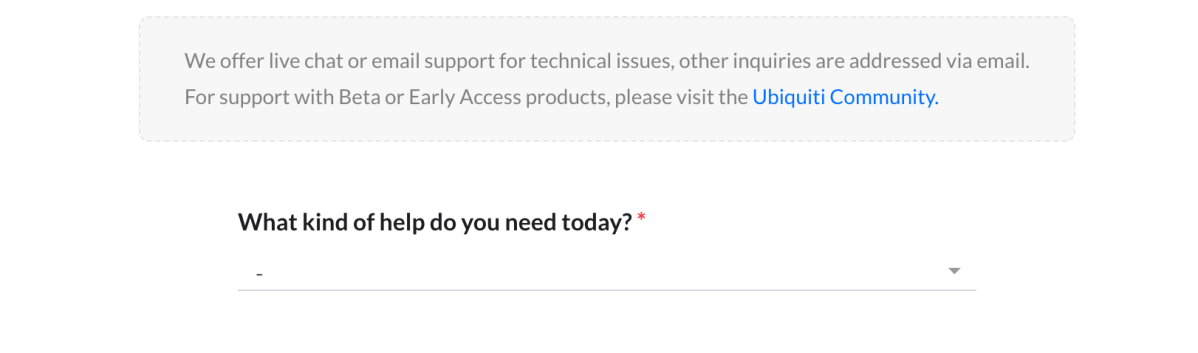
I wrote the previous post reporting my experience trying to log in to my controller host while divorced from the Internet. As expected, it smoked so I opened a ticket.
The various Internet communities can be helpful when I’ve overlooked something or misinterpreted something that is common product knowledge. When something appears to be a design issue, only the designers can help. So I ticketed my experience.
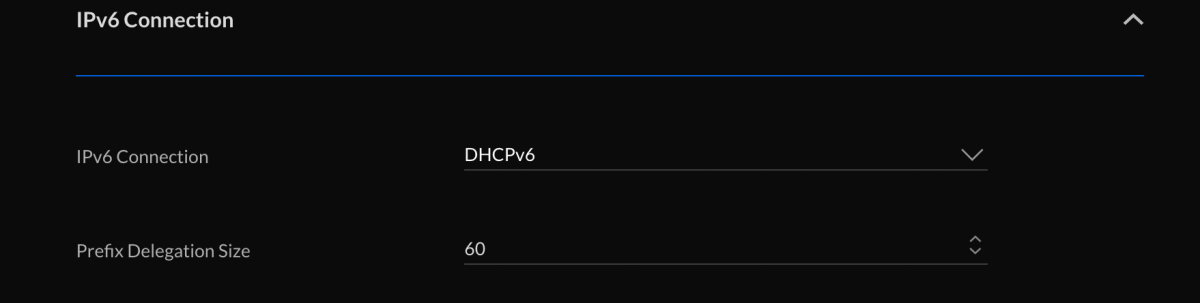
Ubiquity Support has responded with what appears to be the solution to my concern raised in the ticket, that local service should be possible during an Internet fade. Read on for the fix.






You must be logged in to post a comment.